Apple to Address '0.0.0.0' Security Vulnerability in Safari 18
Apple plans to block websites from attempting to send malicious requests to the IP address 0.0.0.0 on macOS Sequoia, according to Forbes. The means the change will be part of Safari 18, which will also be available for macOS Sonoma and macOS Ventura.

This decision comes after researchers from Israeli cybersecurity startup Oligo Security said they discovered a zero-day security vulnerability that allows a malicious actor to access private data on a user's internal private network. The researchers will present their findings this weekend at the DEF CON hacking conference in Las Vegas.
"Exploiting 0.0.0.0-day can let the attacker access the internal private network of the victim, opening a wide range of attack vectors," said Avi Lumelsky, a researcher at Oligo Security.
The researchers responsibly disclosed the vulnerability to Apple, Google, and Mozilla. More details are available on the AppSec Village website.
macOS Sequoia and Safari 18 are currently in beta and will be widely released later this year.
Popular Stories
While the iPhone 17 Pro and iPhone 17 Pro Max are not expected to launch until September, there are already plenty of rumors about the devices.
Below, we recap key changes rumored for the iPhone 17 Pro models as of April 2025:
Aluminum frame: iPhone 17 Pro models are rumored to have an aluminum frame, whereas the iPhone 15 Pro and iPhone 16 Pro models have a titanium frame, and the iPhone ...
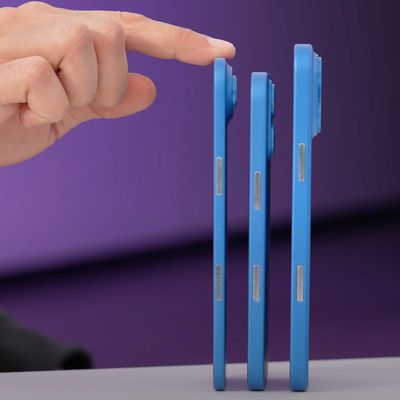
If you missed the video showing dummy models of Apple's all-new super thin iPhone 17 Air that's expected later this year, Sonny Dickson this morning shared some further images of the device in close alignment with the other dummy models in the iPhone 17 lineup, indicating just how thin it is likely to be in comparison.
The iPhone 17 Air is expected to be around 5.5mm thick – with a thicker ...
While the so-called "iPhone 17 Air" is not expected to launch until September, there are already plenty of rumors about the ultra-thin device.
Overall, the iPhone 17 Air sounds like a mixed bag. While the device is expected to have an impressively thin and light design, rumors indicate it will have some compromises compared to iPhone 17 Pro models, including only a single rear camera, a...
Despite being more than two years old, Apple's AirPods Pro 2 still dominate the premium wireless‑earbud space, thanks to a potent mix of top‑tier audio, class‑leading noise cancellation, and Apple's habit of delivering major new features through software updates. With AirPods Pro 3 widely expected to arrive in 2025, prospective buyers now face a familiar dilemma: snap up the proven...
Apple plans to release an all-new super thin iPhone this year, debuting it alongside the iPhone 17, iPhone 17 Pro, and iPhone 17 Pro Max. We've seen pictures of dummy models, cases, and renders with the design, but Lewis Hilsenteger of Unbox Therapy today showed off newer dummy models that give us a better idea of just how thin the "iPhone 17 Air" will be.
The iPhone 17 Air is expected to be ...
Starting today, April 24, Apple Stores around the world are giving away a special pin for free to customers who request one, while supplies last.
Photo Credit: Filip Chudzinski
The enamel pin's design is inspired by the Global Close Your Rings Day award in the Activity app, which Apple Watch users can receive by closing all three Activity rings today. The limited-edition pin is the physical...
Apple's $570 million fine from the EU has triggered a sharp rebuke from the White House, which called the fine a form of economic extortion, Reuters reports.
The fine was announced on Wednesday by the European Commission, following a formal investigation into Apple's compliance with the bloc's Digital Markets Act (DMA), a landmark piece of legislation aimed at curbing the market dominance of ...
When an iPad running iPadOS 19 is connected to a Magic Keyboard, a macOS-like menu bar will appear on the screen, according to the leaker Majin Bu.
This change would further blur the lines between the iPad and the Mac. Bloomberg's Mark Gurman previously claimed that iPadOS 19 will be "more like macOS," with unspecified improvements to productivity, multitasking, and app window management,...
![]()