Apple Launches Security Research Device Program to Give Bug Hunters Deeper OS Access to Find Vulnerabilities
Apple is today launching a new Apple Security Research Device Program that's designed to provide security researchers with special iPhones that are dedicated to security research with unique code execution and containment policies.
Apple last year said it would be providing security researchers with access to "special" iPhones that would make it easier for them to find security vulnerabilities and weaknesses to make iOS devices more secure, which appears to be the program that's rolling out now.
The iPhones that Apple is providing to security researchers are less locked down than consumer devices and will make it easier to find serious security vulnerabilities.
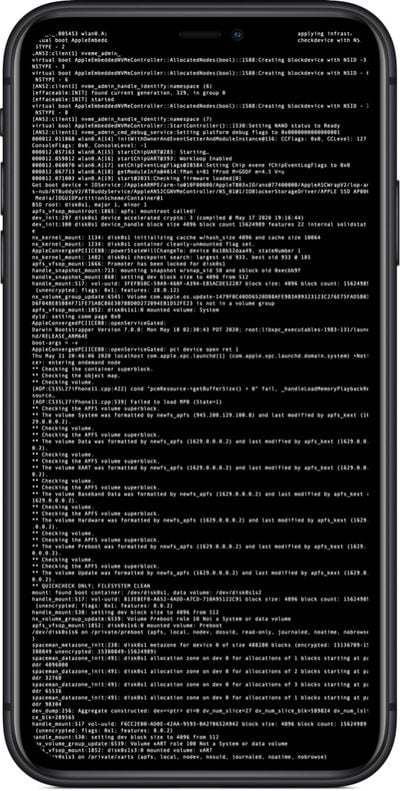
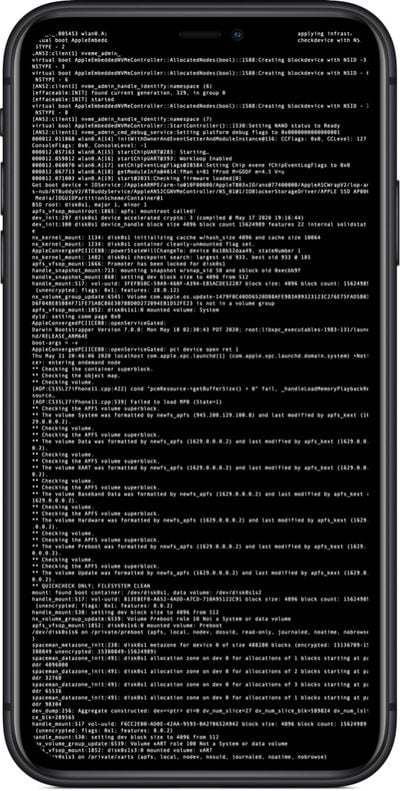
Apple says the Security Research Device (SRD) offers shell access and can run any tools or entitlements, but other than that, it behaves similarly to a standard iPhone. SRDs are provided to security researchers on a 12-month renewable basis and remain Apple property. Bugs discovered with the SRD must be "promptly" reported to Apple or a relevant third-party.
If you use the SRD to find, test, validate, verify, or confirm a vulnerability, you must promptly report it to Apple and, if the bug is in third-party code, to the appropriate third party. If you didn't use the SRD for any aspect of your work with a vulnerability, Apple strongly encourages (and rewards, through the Apple Security Bounty) that you report the vulnerability, but you are not required to do so.
If you report a vulnerability affecting Apple products, Apple will provide you with a publication date (usually the date on which Apple releases the update to resolve the issue). Apple will work in good faith to resolve each vulnerability as soon as practical. Until the publication date, you cannot discuss the vulnerability with others.
Apple is accepting applications for the Security Research Device Program. Requirements include being in the Apple Developer Program, and having a track record finding security issues on Apple platforms.
Those that participate in the program will have access to extensive documentation and a dedicated forum with Apple engineers, with Apple telling TechCrunch that it wants the program to be a collaboration.
The Security Research Device Program will run alongside the bug bounty program, and hackers can file bug reports with Apple and receive payouts of up to $1 million, with bonuses possible for the worst vulnerabilities.
Popular Stories
U.S. President Donald Trump on Wednesday announced that steep tariffs will be applied to imports from many countries, starting April 9. The tariffs could have a significant impact on Apple, as the company assembles the majority of iPhones in China, and products imported to the U.S. from China will be subject to a 54% tariff.
iPhone prices could increase by up to 43% in the U.S. due to the...
If you have an older Apple device that you've been considering upgrading, you're probably wondering how the newly announced tariffs might impact prices going forward, and whether it's worth buying now before there's a price hike.
Given analyst and economist responses to the tariffs, market panic, and Trump's stance on the current financial chaos, the answer is that making a purchase...
iOS 19 will not be available on the iPhone XR, iPhone XS, or the iPhone XS Max, according a private account on social media site X that has accurately provided information on device compatibility in the past.
The iPhone XR, iPhone XS, and iPhone XS Max all have an A12 Bionic chip, so it looks like iOS 19 will discontinue support for that chip. All other iPhones that run iOS 18 are expected...
Apple is reportedly planning a major upgrade to the Telephoto camera in the iPhone 17 Pro, and while it may seem like a step back on paper, the change could actually improve real-world usability, if one leaker's claims are anything to go by.
According to Majin Bu, the iPhone 17 Pro will feature a new Telephoto lens with a 48MP sensor, up from the current 12MP sensor found in the iPhone 16...
Apple has released iOS 18.4, bringing further refinements to Apple Intelligence features, a neat new capability to iPhone 15 Pro devices, new emoji, and more.
While not quite as packed with new features as Apple's preceding iOS 18 point releases, iOS 18.4 still introduces enhancements that aim to make your iPhone smarter and more intuitive. Below, we've listed 12 new things your iPhone ...
While the iPhone 17 Pro and iPhone 17 Pro Max are not expected to launch until September, there are already plenty of rumors about the devices.
Below, we recap key changes rumored for the iPhone 17 Pro models as of March 2025:
Aluminum frame: iPhone 17 Pro models are rumored to have an aluminum frame, whereas the iPhone 15 Pro and iPhone 16 Pro models have a titanium frame, and the iPhone ...