Now Patched 'Sign in With Apple' Bug Left Users Open to Attack
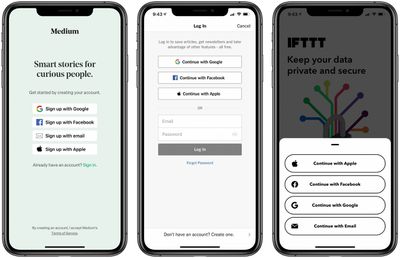
Researcher Bhavuk Jain in April discovered a critical Sign in With Apple vulnerability that could have resulted in a takeover of some user accounts. The bug was specific to third party apps that used Sign in With Apple and didn't implement additional security measures.
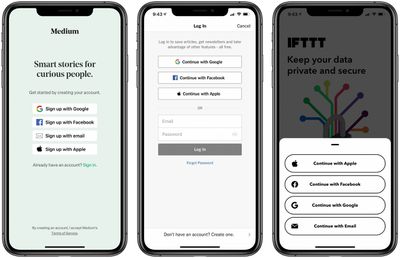
Jain notes that Sign in With Apple works by authenticating a user through a JWT (JSON Web Token) or a code that's generated by Apple's server. Apple then gives users the option to share either the email tied to their Apple ID or a private relay email address,which creates a JWT that's used to log in a user.
Jain then discovered that once JWTs for both Apple ID emails and private relay email addresses were requested and the token's signature was verified using Apple's public key, it "showed as valid." Should the bug have not been discovered, a JWT could be created and used to gain access to one's account.
In an interview with The Hacker News, Jain spoke about the severity of the bug:
The impact of the this vulnerability was quite critical as it could have allowed a full account takeover. Many developers have integrated Sign in with Apple since it is mandatory for applications that support other social logins. To name a few that use Sign in with Apple - Dropbox, Spotify, Airbnb, Giphy (now acquired by Facebook).
According to Jain, Apple conducted an investigation and concluded that no accounts were compromised using this method before the vulnerability was patched. Jain was paid $100,000 by Apple under its Apple Security Bounty Program for reporting the bug.
Popular Stories
While the iPhone 17 Pro and iPhone 17 Pro Max are not expected to launch until September, there are already plenty of rumors about the devices.
Below, we recap key changes rumored for the iPhone 17 Pro models as of April 2025:
Aluminum frame: iPhone 17 Pro models are rumored to have an aluminum frame, whereas the iPhone 15 Pro and iPhone 16 Pro models have a titanium frame, and the iPhone ...
Apple may have updated several iPads and Macs late last year and early this year, but there are still multiple new devices that we're looking forward to seeing in 2025. Most will come in September or October, but there could be a few surprises before then.
We've rounded up a list of everything that we're still waiting to see from Apple in 2025.
iPhone 17, 17 Air, and 17 Pro - We get...
Apple's upcoming foldable iPhone (or "iPhone Fold") will feature two screens as part of its book-style design, and a Chinese leaker claims to know the resolutions for both of them.
According to the Weibo-based account Digital Chat Station, the inner display, which is approximately 7.76 inches, will use a 2,713 x 1,920 resolution and feature "under-screen camera technology." Meanwhile, the...
A common complaint about the iPad Pro is that the iPadOS software platform fails to fully take advantage of the device's powerful hardware.
That could soon change.
Bloomberg's Mark Gurman today said that iPadOS 19 will be "more like macOS."
Gurman said that iPadOS 19 will be "more like a Mac" in three ways:Improved productivity
Improved multitasking
Improved app window management...
Apple in October 2024 overhauled its 14-inch and 16-inch MacBook Pro models, adding M4, M4 Pro, and M4 Max chips, Thunderbolt 5 ports on higher-end models, display changes, and more. That's quite a lot of updates in one go, but if you think this means a further major refresh for the MacBook Pro is now several years away, think again.
Bloomberg's Mark Gurman has said he expects only a small...
Apple is working on a new version of the Vision Pro with two key advantages over the current model, according to Bloomberg's Mark Gurman.
Specifically, in his Power On newsletter today, Gurman said Apple is developing a new headset that is both lighter and less expensive than the current Vision Pro, which starts at $3,499 in the U.S. and weighs up to 1.5 pounds.
Gurman said Apple is also...
On this week's episode of The MacRumors Show, we catch up on the latest iOS 19 and watchOS 12 rumors, upcoming devices, and more.
Subscribe to The MacRumors Show YouTube channel for more videos
Detailed new renders from leaker Jon Prosser claim to provide the best look yet at the complete redesign rumored to arrive in iOS 19, showing more rounded elements, lighting effects, translucency, and...
It was a big week for leaks and rumors in the Apple world, with fresh claims about iOS 19, the iPhone 17 Pro, and even the 20th anniversary iPhone coming a couple of years from now.
Sources also spilled the tea on the inner turmoil at Apple around the Apple Intelligence-driven Siri revamp that has seen significant delays, so read on below for all the details on these stories and more!
iOS ...
Apple and other electronics manufacturers have received a break from Trump's reciprocal tariffs, with the U.S. Customs and Border Protection agency sharing a long list of products excluded from the levies last night.
iPhones, Macs, iPads, Apple Watch, and other Apple devices will not be subject to the 125 percent tariffs that have been put in place on imported Chinese goods, nor will Apple...