Safari AutoFill Security Issue Rears Its Head Once Again
Back in July, security researcher Jeremiah Grossman revealed a security issue that could allow malicious parties to take advantage of Safari's AutoFill feature to extract personal information from users' Address Book entries. At the time, Grossman reported that his report to Apple had gone essentially unacknowledged for nearly a month, but just six days later Apple released Safari 5.0.1 and 4.1.1 to address the problem.
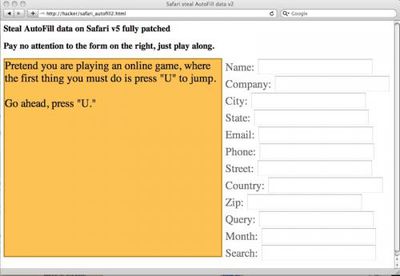
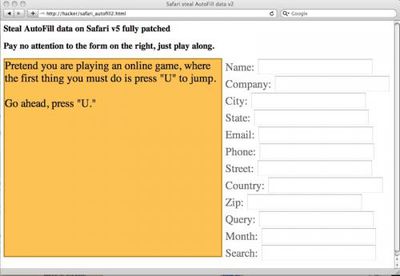 Screenshot of Grossman's proof-of-concept test of new AutoFill exploit
Screenshot of Grossman's proof-of-concept test of new AutoFill exploitGrossman
now reports that he has discovered another similar AutoFill security issue that, while requiring the malicious party to trick users into providing a pair of keystrokes rather than being completely automated as in the previous exploit, offers an even more efficient means for users' personal information to be obtained.
To perform our attack requires tiny bit of end-user trickery. Two button presses to be precise. A malicious website detects (ie: IP address) the country the victim is from. For our purposes here we'll assume the "US." The attacker invisibly (CSS transparency) sets up the aforementioned form and forces the keystroke focus into the country element. Notice how this is done in the video on the right side of the screen, which only visible for demonstration purposes. Next the attacker entices the victim to type "U" (first character of "US") and then press "TAB." And BAM! That's it! Data stolen.
Grossman relates that he notified Apple of the newly-discovered exploit via email on August 10th and again a few days later. One week after that, he received a phone call from an Apple product security engineer with whom he had a "productive chat" about how the original vulnerability report from June had been handled, only to discover at the end of the conversation that the engineer had no idea that Grossman had reported the second issue a week and half prior.
As with the earlier exploit, users can protect themselves by simply turning off the AutoFill option to automatically populate forms with information from their Address Book cards. Grossman notes, however, that he is unsure how Apple plans to address the vulnerability while still maintaining the convenience of the AutoFill feature. While Apple's previous patch allowed Safari to automatically differentiate from the automated JavaScript-simulated keystrokes from real keystrokes, thus thwarting the original exploit, the new exploit relies on tricking the user into actually entering the necessary keystroke, a tactic that could be more difficult to address.
Popular Stories
Apple should unveil the iPhone 17 series in September, and there might be one bigger difference between the Pro and Pro Max models this year.
As always, the Pro Max model will be larger than the Pro model:iPhone 17 Pro: 6.3-inch display
iPhone 17 Pro Max: 6.9-inch displayGiven the Pro Max is physically larger than the Pro, it has more internal space, allowing for a larger battery and...
Since the iPhone X in 2017, all of Apple's highest-end iPhone models have featured either stainless steel or titanium frames, but it has now been rumored that this design decision will be coming to an end with the iPhone 17 Pro models later this year.
In a post on Chinese social media platform Weibo today, the account Instant Digital said that the iPhone 17 Pro models will have an aluminum...
The calendar has turned to July, meaning that 2025 is now more than half over. And while the summer months are often quiet for Apple, the company still has more than a dozen products coming later this year, according to rumors.
Below, we have outlined at least 15 new Apple products that are expected to launch later this year, along with key rumored features for each.
iPhone 17 Series
iPho...
Apple is continuing to refine and update iOS 26, and beta three features smaller changes than we saw in beta 2, plus further tweaks to the Liquid Glass design. Apple is gearing up for the next phase of beta testing, and the company has promised that a public beta is set to come out in July.
Transparency
In some apps like Apple Music, Podcasts, and the App Store, Apple has toned down the...
In 2020, Apple added a digital car key feature to its Wallet app, allowing users to lock, unlock, and start a compatible vehicle with an iPhone or Apple Watch. The feature is currently offered by select automakers, including Audi, BMW, Hyundai, Kia, Genesis, Mercedes-Benz, Volvo, and a handful of others, and it is set to expand further.
Apple has a web page with a list of vehicle models that ...
Apple's next-generation iPhone 17 Pro and iPhone 17 Pro Max are just over two months away, and there are plenty of rumors about the devices.
Below, we recap key changes rumored for the iPhone 17 Pro models.
Latest Rumors
These rumors surfaced in June and July:Apple logo repositioned: Apple's logo may have a lower position on the back of the iPhone 17 Pro models, compared to previous...
New renders today provide the best look yet relocated Apple logo and redesigned MagSafe magnet array of the iPhone 17 Pro and iPhone 17 Pro Max.
Image via Majin Bu.
Several of the design changes coming to the iPhone 17 Pro model have been rumored for some time, such as the elongated camera bump that spans the full width of the device, with the LiDAR Scanner and flash moving to the right side.
...
iPhone 17 models will feature a redesigned Dynamic Island user interface, according to a post today from Digital Chat Station, an account with more than three million followers on Chinese social media platform Weibo. The account has accurately leaked some information regarding future Apple products in the past.
The account did not share any specific details about the alleged changes that are ...
Amazon is back with its annual summertime Prime Day event, lasting for four days from July 8-11, the longest Prime Day yet. As it does every year, Prime Day offers shoppers a huge selection of deals across Amazon's storefront. With the event now underway, we're tracking numerous all-time low prices on Apple gear right now.
Note: MacRumors is an affiliate partner with Amazon. When you click a...